Process & Port Analyzer – Network & Process Monitor for Windows
A free Windows utility for deep inspection of running processes, active TCP/UDP connections, listening ports, Windows Firewall rules, and live packet capture — all using native Windows APIs, no third-party libraries required.
Features
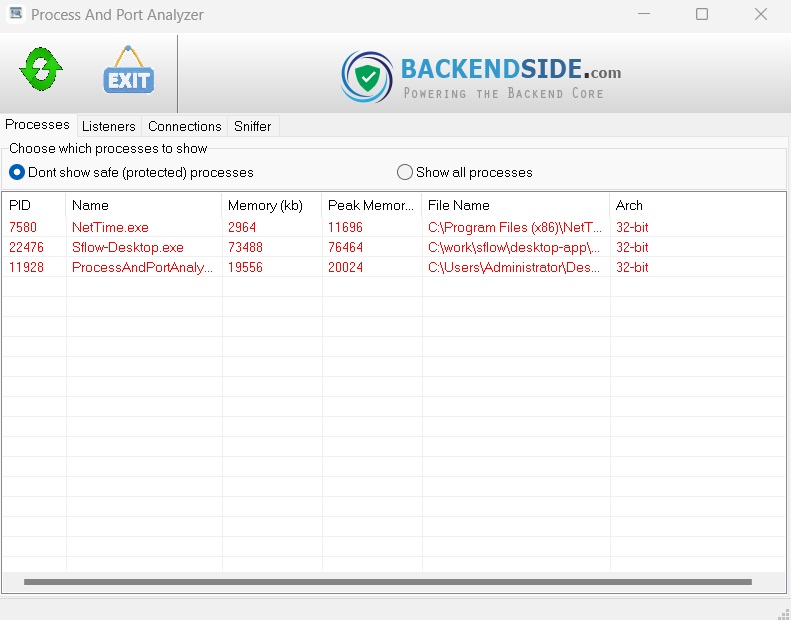
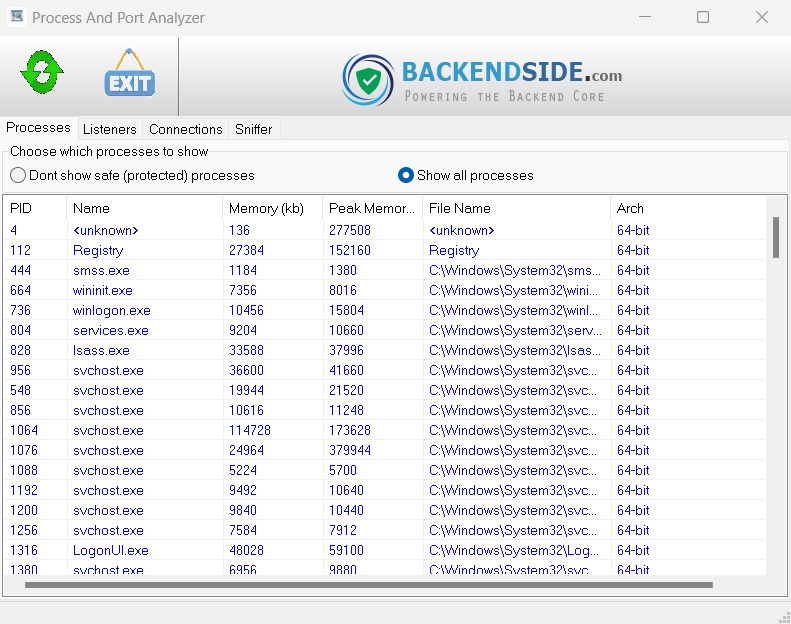
⚙️ Running Process Viewer
Lists all running processes with PID, process name, and full executable file path. Double-click any process to open a detailed module view showing every DLL and file loaded by that process, with full paths.
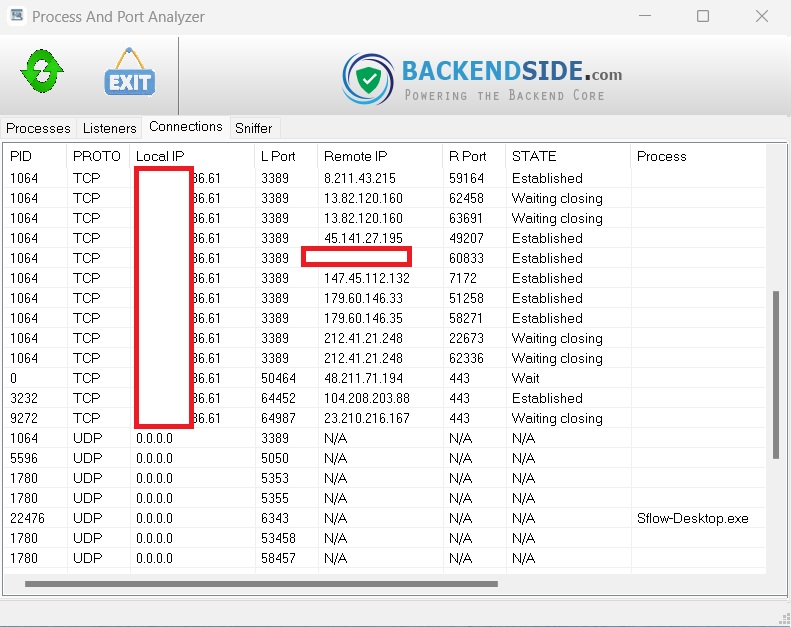
🔌 Active TCP/UDP Connections
Displays all active TCP and UDP connections in real time — showing PID, protocol, local IP/port, remote IP/port, connection state (e.g. ESTABLISHED, TIME_WAIT), process name, and full executable path.
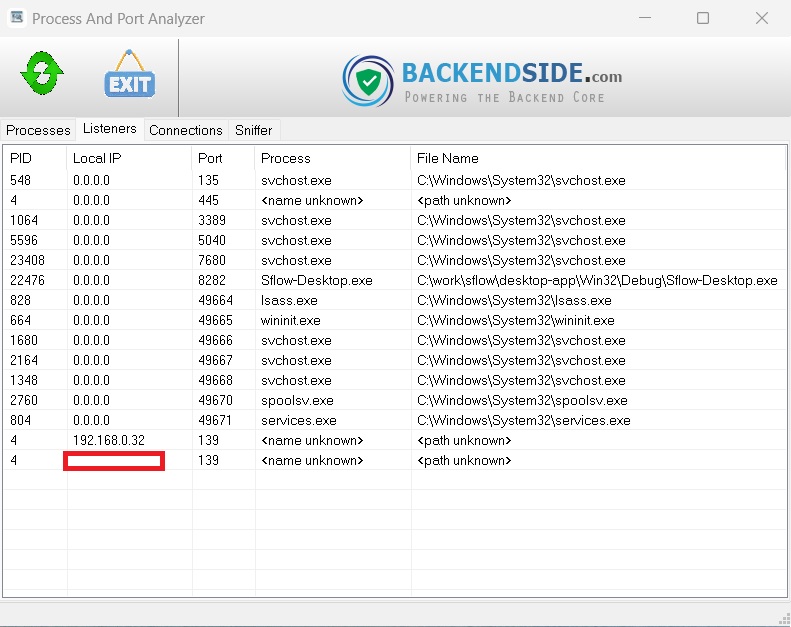
👂 Listening Ports Viewer
Shows all TCP and UDP ports currently in a listening state, including the owning PID, process name, and full file path — making it easy to identify which services are accepting inbound connections.
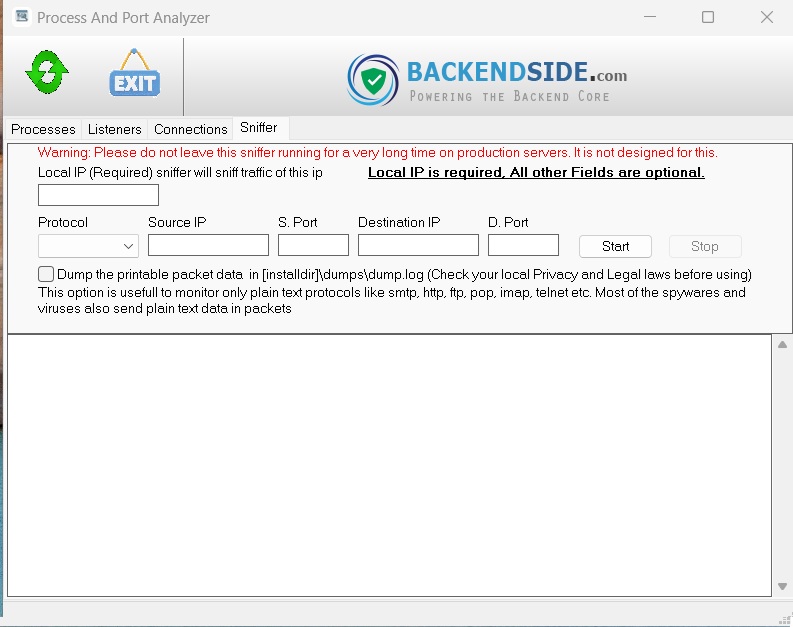
📡 Packet Sniffer
Built-in raw packet sniffer using native Winsock APIs in promiscuous mode. Captures and decodes TCP, UDP, ICMP, and IGMP packets — showing protocol, source/destination IP and port, packet size, TTL, and TCP flags (SYN, ACK, FIN, RST, etc.).
🔎 Packet Filtering
Filter captured packets by source IP, destination IP, source port, and destination port. Only matching traffic is displayed — making it easy to isolate specific connections in a busy network.
💾 Packet Hex Dump
Optionally save captured packets to a dump.log file with timestamped entries showing protocol, source/destination, packet size, and a full hex + ASCII side-by-side dump of each packet's raw content.
🛡️ Windows Firewall Rule Manager
View, create, enable, and disable Windows Firewall rules directly from the app. Create inbound or outbound rules for TCP, UDP, ICMP, or any protocol, with specific local/remote IPs and ports — or block a connection with one right-click.
🚫 Block Connection from Context Menu
Right-click any active connection and choose "Block this connection" to instantly open the firewall rule creator, pre-filled with the connection's IP, port, and protocol — creating a block rule in seconds.
🔃 Sortable Columns
All list views support column sorting — click any column header to sort ascending or descending. Numeric columns (like PID and port numbers) sort as integers, not text, for accurate ordering.
🔒 No External Dependencies
Everything runs on native Windows APIs — iphlpapi, psapi, Winsock2, and the Windows Firewall COM interface. No WinPcap, Npcap, or any third-party library required.
Common Uses
🕵️ Security Auditing
Identify unexpected outbound connections, suspicious listening ports, or unknown processes communicating on your network — without needing any external tools.
🖥️ Server Monitoring
Get a full picture of what's running and listening on a Windows server — ideal for system administrators checking service health or investigating unexpected activity.
🧑💻 Developer Network Debugging
Trace which ports your application is using, inspect raw TCP/UDP packets during development, and verify your app's network behaviour with the built-in packet capture and hex dump.
🔥 Firewall Troubleshooting
View all existing Windows Firewall rules in one place, enable or disable rules on the fly, and quickly create precise block or allow rules based on live connection data.
Screenshots
Latest Release
Version 1.0 — January 2026
Initial release — process viewer, TCP/UDP connections, packet sniffer, firewall rule manager.
