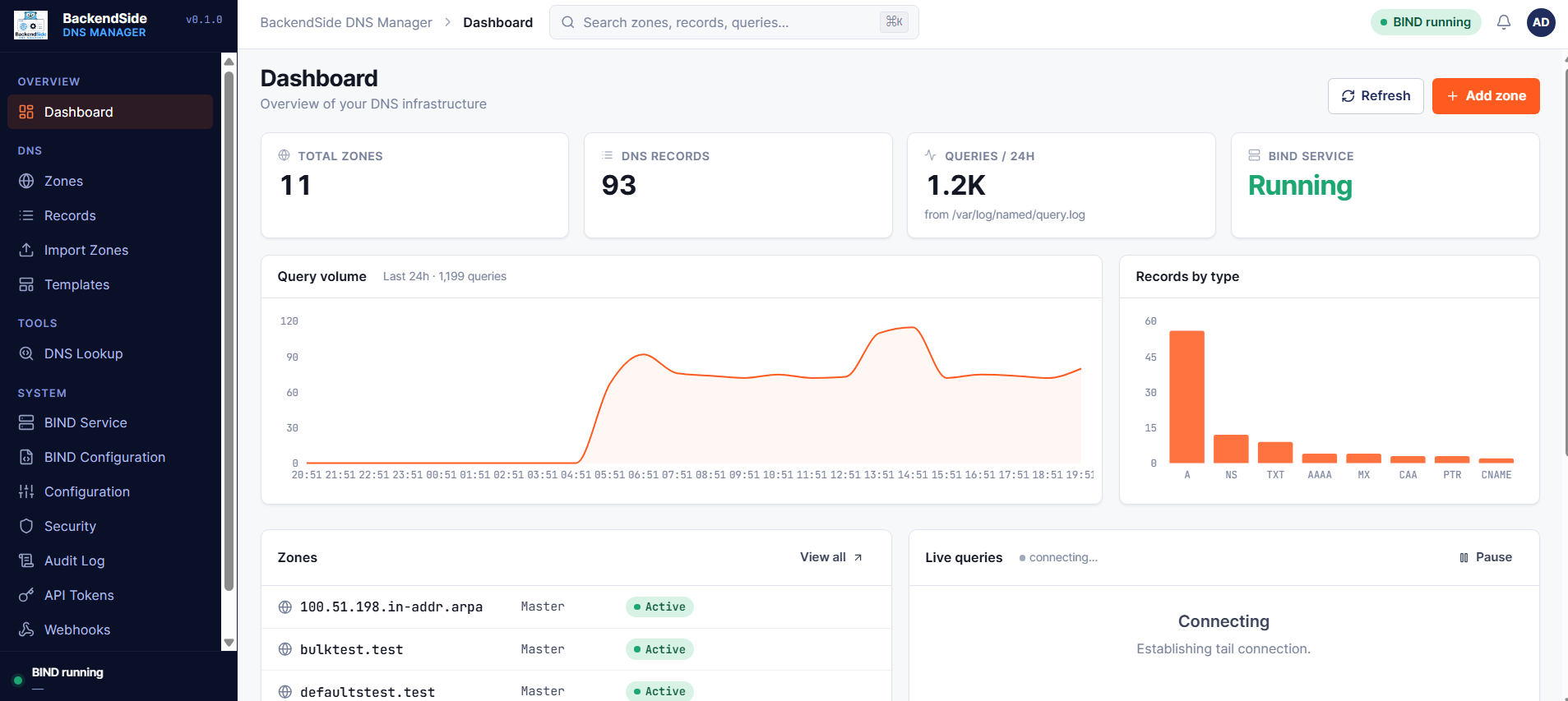
BackendSide DNS Manager – Web-based authoritative DNS management for BIND
BackendSide DNS Manager is a self-hosted, web-based control panel for BIND 9. It manages authoritative zones, records, DNSSEC, webhooks, and import/export workflows — all through a clean dashboard and a complete REST API. No database is required: zones live as ordinary BIND zone files on disk, so your existing tooling and backups continue to work unchanged.
One-click install — from clean Linux server to working DNS in under a minute
You don't need to be a BIND expert. Install the .deb or .rpm on a clean Linux server and the package's professional installer takes care of everything — no manual editing of named.conf, no permission juggling, no chroot puzzles, no follow-up scripts.
In a single apt install or dnf install, the package will:
- Install BIND 9 if it isn't already present, and configure it as an authoritative name server
- Create a dedicated system user, the managed-zones directory, and the writable working directories with the right ownership and SELinux/AppArmor labels
- Add a clean, isolated
includeline to yournamed.conf— so your existing BIND setup keeps working untouched - Generate a strong random API key, JWT signing secret, and config file at
/etc/backendside-dns-manager/config.env - Install the systemd unit, open the service ports, and start everything — both the manager and BIND
Then just open http://<your-server>:8084 in a browser, the elegant first-run setup wizard creates your admin account, and you're managing zones, records, and DNSSEC from a clean web dashboard. Even a junior sysadmin can stand up a production DNS server in minutes — with none of the usual BIND configuration intimidation.
Download BackendSide DNS Manager v0.1.0 (Build 041) for Linux
Packages for Debian/Ubuntu (DEB) and RHEL-based distributions (RPM)
| Distribution | Package | SHA256 Checksum |
|---|---|---|
| DEB Ubuntu 22.04 / 24.04 / Debian 12 and any Debian-based distro with systemd | backendside-dns-manager_0.1.0_041_amd64.deb | f1901fd573e65a72774a55af6609de276c5c20f95c662573f02be7742991186a |
| RPM RHEL 9 / 10 · AlmaLinux 9 / 10 · Rocky 9 / 10 · CentOS Stream 9 | backendside-dns-manager_0.1.0_041_amd64.rpm | e2f3a78e723639921394e1b46e64eea592ba7d43c5f4390eb6b6a44873829496 |
DEB Installation (Ubuntu / Debian) — one command, zero configuration
sudo apt install ./backendside-dns-manager_0.1.0_041_amd64.debThat's it. The installer handles BIND 9 setup, system user, zone directories, named.conf include, API key & JWT secret generation, the systemd unit, and starts both services. Open http://<your-server-ip>:8084 and the setup wizard creates your admin account.
RPM Installation (RHEL / AlmaLinux / Rocky / CentOS) — one command, zero configuration
sudo dnf install ./backendside-dns-manager_0.1.0_041_amd64.rpmThat's it. The installer handles BIND 9 setup, system user, zone directories, named.conf include, API key & JWT secret generation, SELinux contexts, the systemd unit, and starts both services. Open http://<your-server-ip>:8084 and the setup wizard creates your admin account.
include directive that loads only the manager's zones from /var/lib/backendside-dns-manager/zones/. Your existing zones, views, and ACLs are not modified.
Full REST API reference — build, automate, integrate
Every action in the web UI is also a documented JSON API call. Drive zones, records, DNSSEC, imports and bulk operations from CI, Terraform, monitoring, or your own scripts — with side-by-side cURL and PHP examples for every endpoint.
Read the API ReferenceFeatures
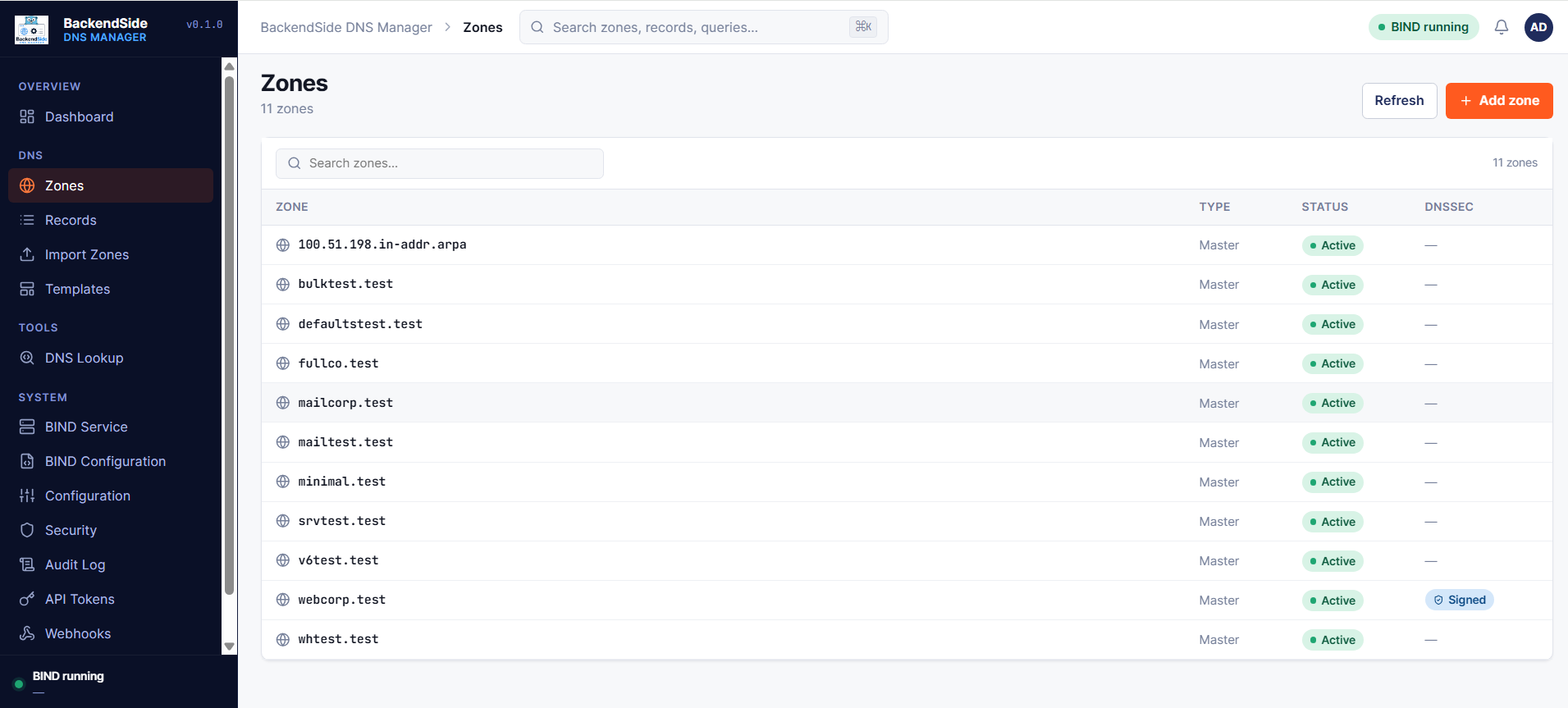
- Zone management: Create, edit, soft-delete, and bulk-operate on authoritative zones — with automatic SOA serial bumping
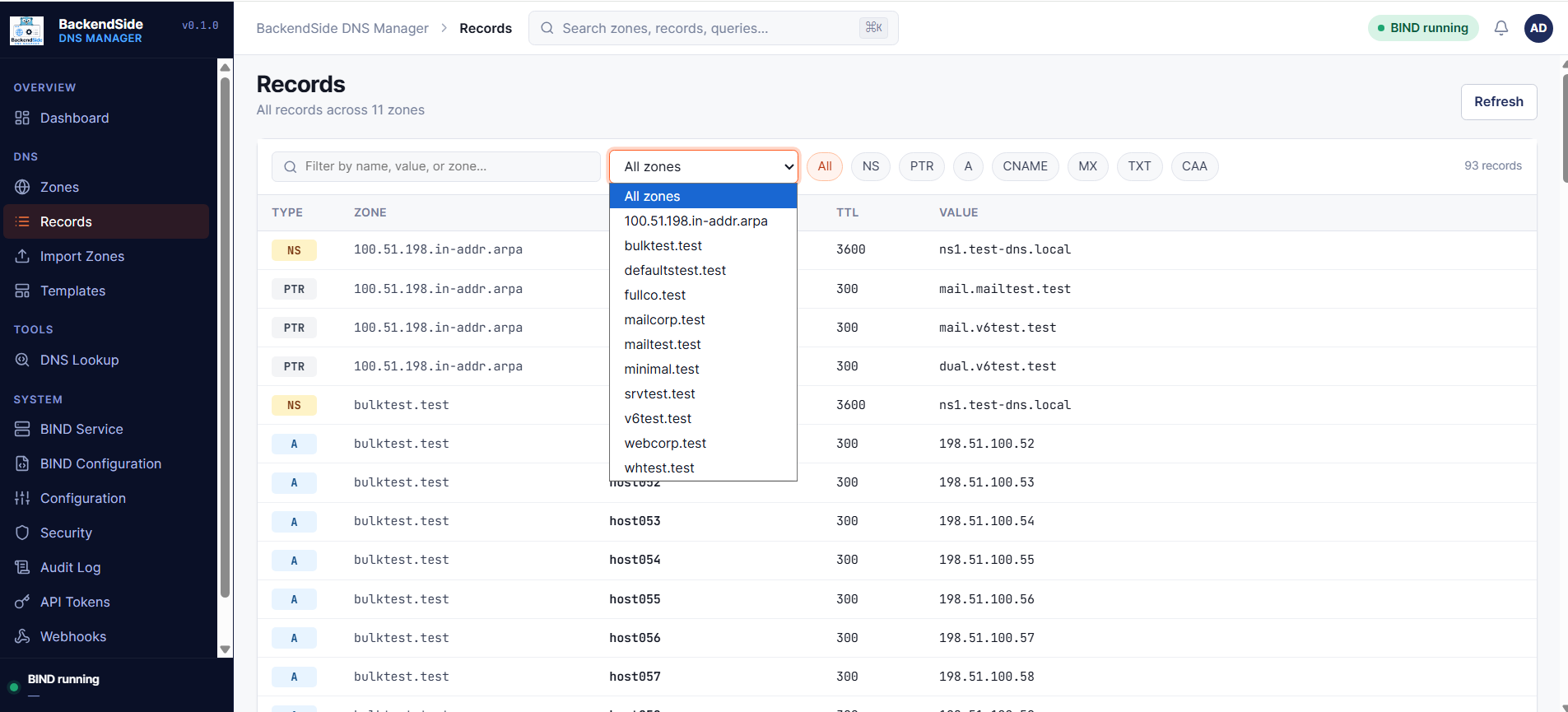
- Record types: A, AAAA, CNAME, MX, TXT (multi-string & long), NS, PTR, SRV, CAA — with per-record TTL and validation
- DNSSEC: One-click sign/unsign per zone using BIND's KASP — KSK/CSK key tags and algorithm visible in the UI; keys stored under BIND's standard key directory
- Import & export: Bulk import standard zone-file format; export individual zones or a tarball of all managed zones
- Webhooks: Subscribe external systems to zone & record events with per-webhook event filters (created / updated / deleted / signed) and HMAC signing
- REST API: Every UI action is also a documented JSON API call — authenticated via X-API-Key header or Bearer JWT token
- Authentication: Username + password login with bcrypt hashing, 24-hour JWT sessions, and a first-run setup wizard
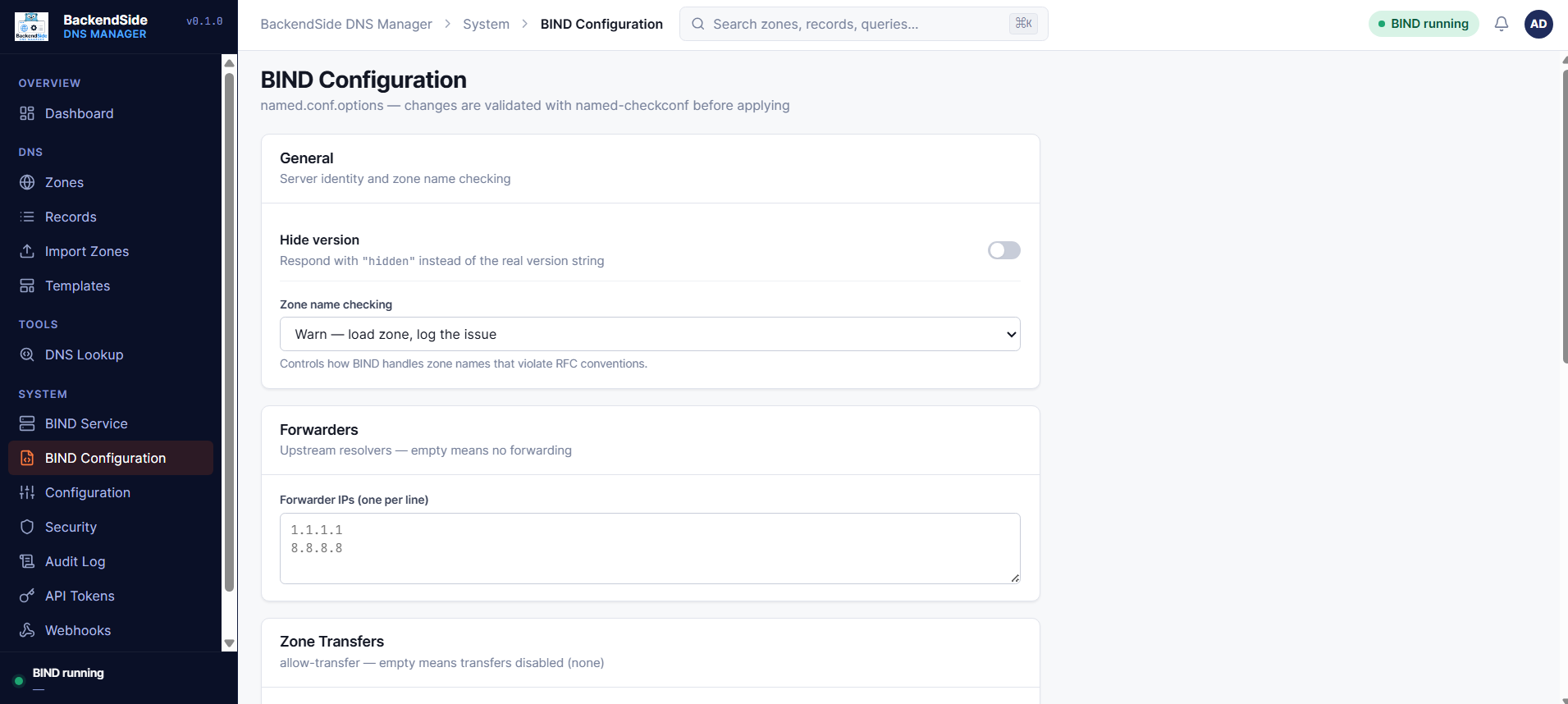
- SSL / TLS: Optional HTTPS listener on port 8085 — upload your certificate or paste it from the settings page
- Zero database: All state lives in BIND zone files and a small KEY=VALUE config file — trivial to back up, version, and audit
- Single self-contained binary: Web UI and API are embedded in one native executable — no separate web server, no runtime dependencies, no language toolchain on the host
- One-click installer: The
.deb/.rpmpostinstall configures BIND, generates secrets, installs the systemd unit, and starts everything — no manual steps - Runs as a systemd service: Starts automatically on boot, with logs in
journalctl -u backendside-dns-manager
OS: Ubuntu 22.04 / 24.04, Debian 12, RHEL / AlmaLinux / Rocky 9 or 10, CentOS Stream 9 (x86_64)
BIND: 9.18 or later, installed on the same host
Ports: 8084 (HTTP) and optionally 8085 (HTTPS) reachable from your admin network
Software Screenshots